Yesterday, Anthropic announced Claude Mythos Preview, their most powerful model to date, and then did something unprecedented: they refused to release it.
Mythos can autonomously discover zero-day vulnerabilities in production software, write working exploits, and chain multiple flaws into full attack sequences. It found thousands of zero-days across every major operating system and every major web browser, including bugs that have been hiding in plain sight for decades.
If you ship code, yesterday changed what your next six months look like.
What Mythos Actually Did
The numbers are hard to process the first time you read them.
On the Firefox 147 exploit benchmark, Mythos developed working exploits 181 times. Claude Opus 4.6, Anthropic's previous best, managed it twice. That's a 90x improvement in exploit development capability.
On OSS-Fuzz corpus testing, Mythos achieved 595 crashes at tiers 1-2 and full control flow hijack on ten separate, fully patched targets at tier 5. Opus 4.6 topped out at around 175 crashes, tier 1 only.
On CyberGym, Mythos scored 83.1% versus 66.6% for Opus 4.6.
In one test, the model wrote a complete browser exploit that chained together four vulnerabilities, building a complex JIT heap spray that escaped both renderer and OS sandboxes.
But the headline number isn't a benchmark score. It's what Mythos found in the wild:
- CVE-2026-4747: A 17-year-old remote code execution vulnerability in FreeBSD's NFS implementation. Unauthenticated. Gives root. Mythos built a 20-gadget ROP chain across multiple packets to exploit it.
- OpenBSD SACK vulnerability: 27 years old. Remote crash affecting firewall infrastructure.
- FFmpeg: A 16-year-old encoding/decoding flaw that five million automated test runs missed.
- Linux kernel: Multiple chained vulnerabilities enabling privilege escalation from user to root.
These discoveries are cheap to run. The FreeBSD vulnerability cost under $50 per individual run. The FFmpeg campaign cost roughly $10,000 total for several hundred runs. A full n-day exploit for a Linux kernel vulnerability cost under $1,000 and took half a day.
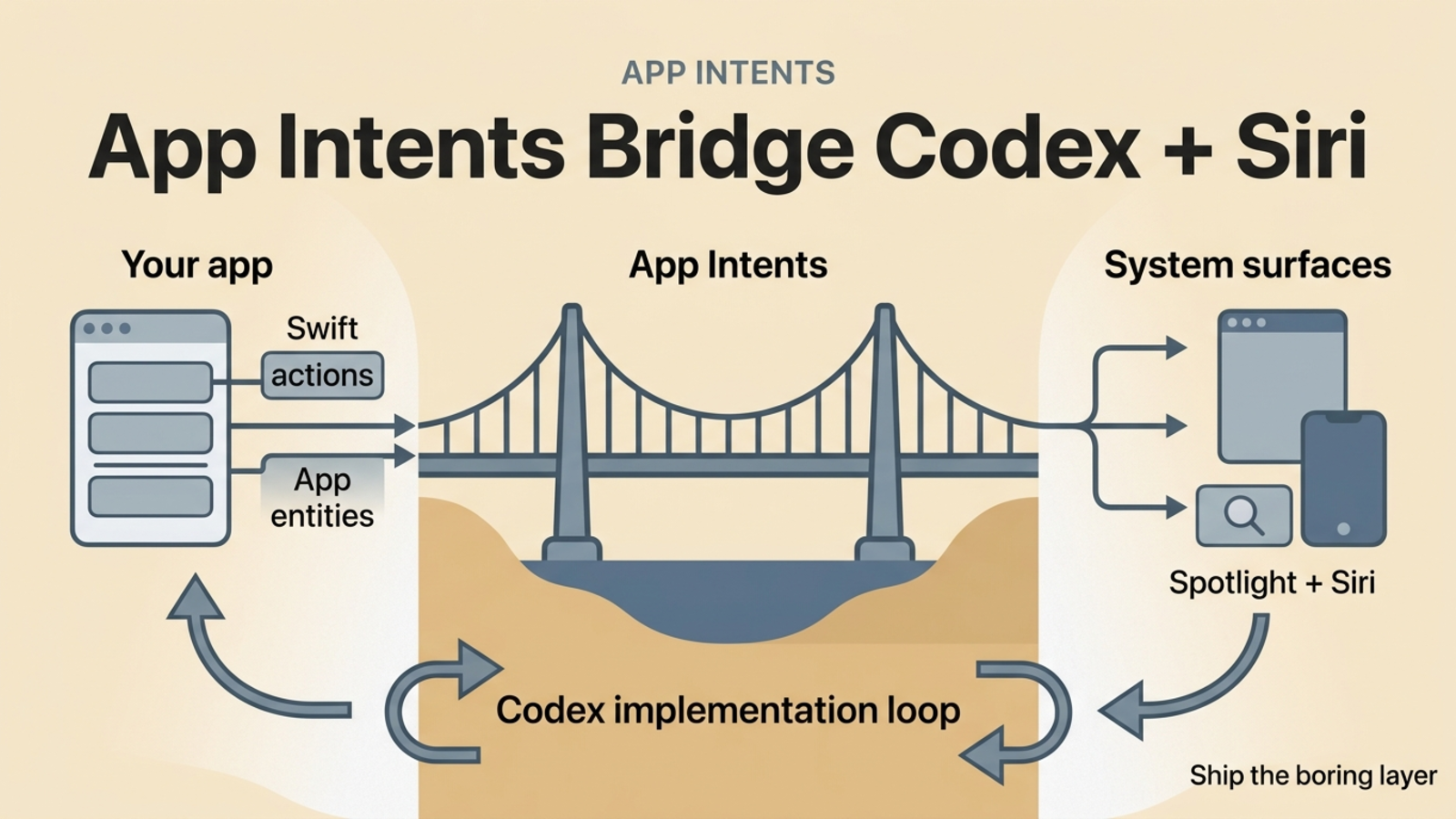
When Dario Amodei described the capability, he was characteristically understated: "We haven't trained it specifically to be good at cyber. We trained it to be good at code, but as a side effect of being good at code, it's also good at cyber."
That side effect found thousands of critical zero-days in software the entire internet depends on.
Project Glasswing
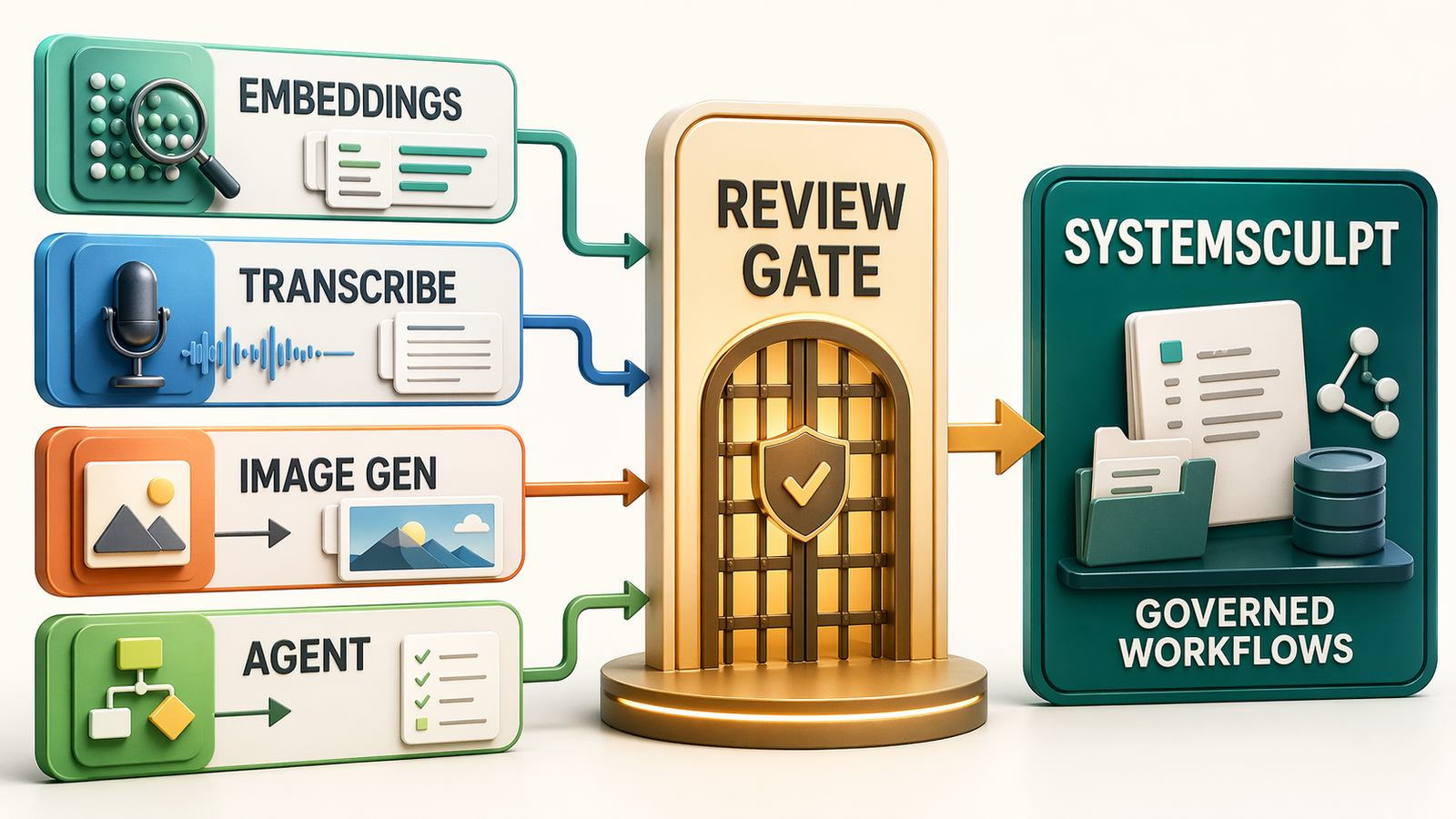
Instead of releasing Mythos publicly, Anthropic launched Project Glasswing: a coordinated security initiative that reads like the entire critical-infrastructure supply chain in one room.
The 12 launch partners: Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, Linux Foundation, Microsoft, NVIDIA, Palo Alto Networks, and Anthropic itself.
Over 40 additional organizations that build or maintain critical software infrastructure have been extended access to scan and secure both first-party and open-source systems.
Anthropic is backing this with real money: up to $100 million in usage credits for Mythos Preview across the effort, plus $4 million in direct donations to open-source security organizations. That breaks down to $2.5 million to Alpha-Omega and OpenSSF through the Linux Foundation and $1.5 million to the Apache Software Foundation.
The disclosure model is deliberate. For some vulnerabilities, patches have already shipped. For others, Anthropic has published cryptographic hashes of the vulnerability details (provable timestamps of discovery) and will reveal specifics only after fixes are in place. Within 90 days, they'll publish a public report on lessons learned.
This is coordinated disclosure at a scale the industry has never seen. It's also an implicit admission: if they released this model without the patch window, the damage would be catastrophic.
As Microsoft's global CISO put it: "As we enter a phase where cybersecurity is no longer bound by purely human capacity, the opportunity to use AI responsibly to improve security and reduce risk at scale is unprecedented."
Every Serious Repo Is About to Go Security-Only
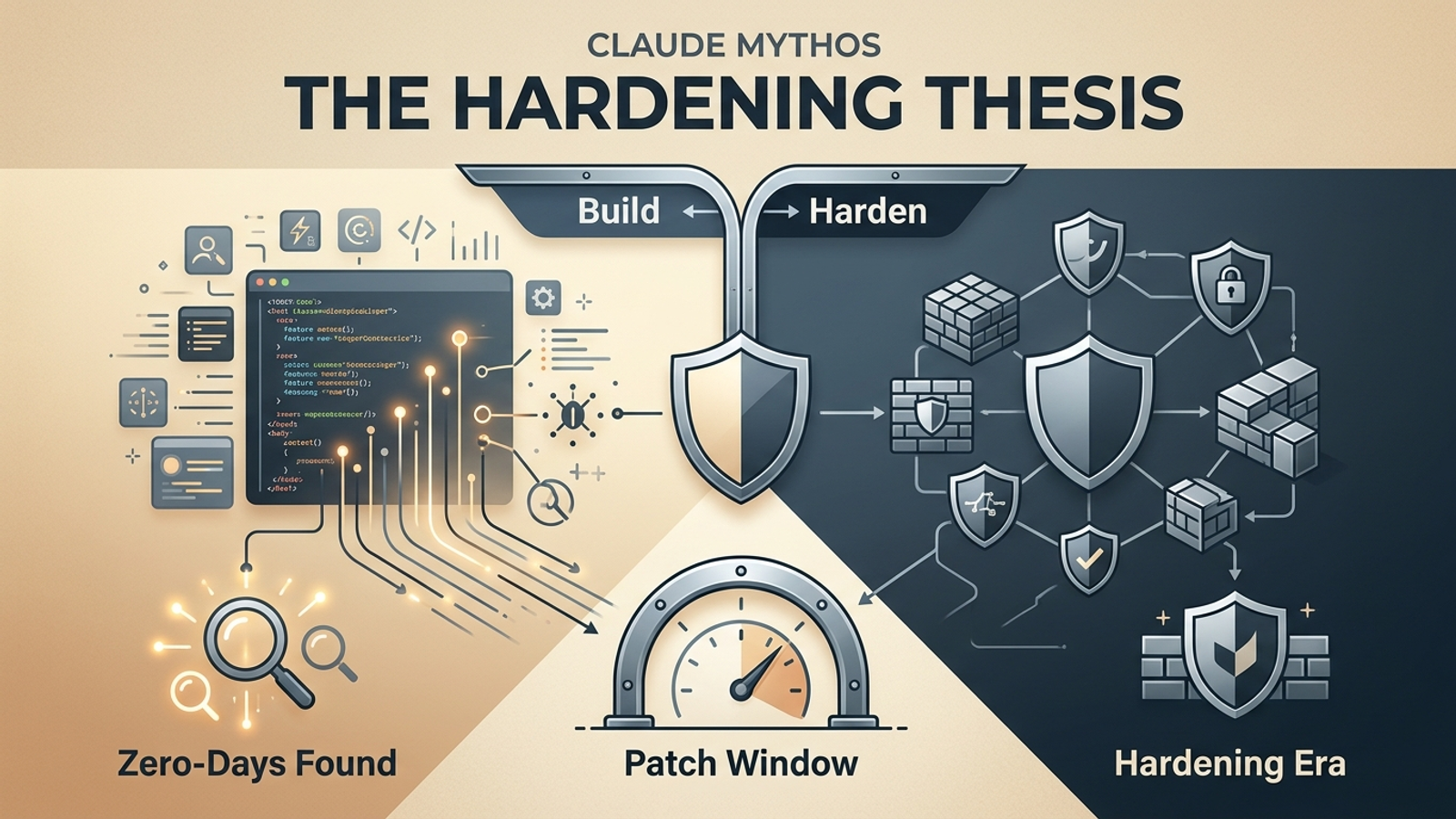
Here's the thesis in one sentence: the feature era just ended, and the hardening era just started.
For the past two years, AI code generation has been an accelerant for building things. New features, new products, new integrations. The toolchain kept improving. Claude Code, Cursor, Copilot, Windsurf. The velocity kept climbing. Most operators I know, myself included, have been riding that wave. Ship faster. Build more. Automate the boring parts.
Mythos changes the math. If an AI can find thousands of critical vulnerabilities in the most scrutinized codebases on Earth (FreeBSD, the Linux kernel, Firefox, OpenBSD), what do you think it'll find in your production code?
I think the rest of 2026 looks like this: most commits in serious repos become security-focused. Dependency audits, infrastructure hardening, access control reviews, input validation passes, CI pipeline security, secrets management, penetration testing with AI-assisted tooling. Not because it's fun. Because the cost of not doing it just went from theoretical to measurable.
The same AI capabilities that found those zero-days will soon be available to everyone. Including adversaries. Project Glasswing buys a head start, not a permanent shield.
My Hardening Checklist at SystemSculpt
I run SystemSculpt, AI-powered tools for Obsidian and workflow automation. It's not a bank. It's not critical infrastructure in the Glasswing sense. But after reading the Mythos risk report, I'm making changes anyway.
This week:
- Full dependency audit across every production service
- Review of all API key management and secrets rotation
- CI pipeline hardening: no permissive flags, no skipped checks
- Input validation pass on every public-facing endpoint
- Supply chain review: every third-party integration gets scrutinized
Call it cautious if you want. I'd call it the new baseline. If Mythos found a 27-year-old vulnerability in OpenBSD, the idea that anyone's code is clean by default is no longer a reasonable assumption.
I'm also rethinking the ratio of feature work to hardening work for the rest of the year. I was running at maybe 80/20 in favor of new features. I expect that to shift closer to 40/60 for the foreseeable future. Not because I want to. Because the risk calculus just changed, and ignoring that change is a choice with consequences.
The Zero-Day Timing Problem
Here's the thought that kept me up last night.
If you're a state actor, or a well-resourced non-state actor, sitting on zero-days you've been saving for the right moment, the Mythos announcement changes your timeline.
Before Mythos, your stockpiled zero-days could sit for years. The software vendor wasn't going to find them through normal testing; they'd been there for decades, after all. You could wait for the optimal moment to deploy them.
After Mythos, the clock is ticking. AI-driven vulnerability discovery means your zero-days have a shelf life now. Project Glasswing is actively scanning the same codebases where your exploits live. Every week that passes, the probability that your hoarded vulnerabilities get discovered and patched goes up.
The rational move? Use them before you lose them.
I hope this isn't what happens. But game theory doesn't care about hope. The incentive structure just shifted toward exploitation on a shorter timeline, which means the patch window matters more than ever. The next few months are the highest-risk period.
This is why Glasswing's "cryptographic hash now, details later" approach matters. It compresses the gap between discovery and patch while maintaining proof of responsible behavior. But it's a race.
The People Who Won't Take This Seriously
There's a cohort (I've talked to some of them) who hear "AI found vulnerabilities" and think: that's a big company problem. I'm a solo dev. Nobody's targeting me.
This is exactly backwards.
Mythos-class capabilities don't find targeted vulnerabilities in specific targets. They find vulnerability classes across entire ecosystems. If your project uses FreeBSD, or links against FFmpeg, or runs on the Linux kernel (and whose doesn't?), you inherit those risks whether you're a Fortune 500 company or a weekend project.
The attack surface doesn't care about your company size. Automated exploit tools don't manually select targets. When these capabilities proliferate (and they will), they'll be pointed at everything, indiscriminately.
The regret will be highest for the people who had time to harden and chose not to because nothing had happened to them yet. "Nothing has happened to me" is not a security strategy. It's a countdown.
What Comes Next
The hardening thesis is pragmatic. AI just handed defenders a genuine capability upgrade; Glasswing proves that. But it also compressed the timeline for everyone else. The window between "vulnerability exists" and "vulnerability gets found" just collapsed from decades to days.
If you ship code, your next six months look different than your last six months. That's not a prediction; it's already happening. The commits are changing. The priorities are shifting. The question isn't whether to start hardening. It's whether you start now, while there's still a head start, or later, when there isn't one.
If you want to see how I'm applying these principles in practice, the SystemSculpt plugin and resources library are where this work lands first.